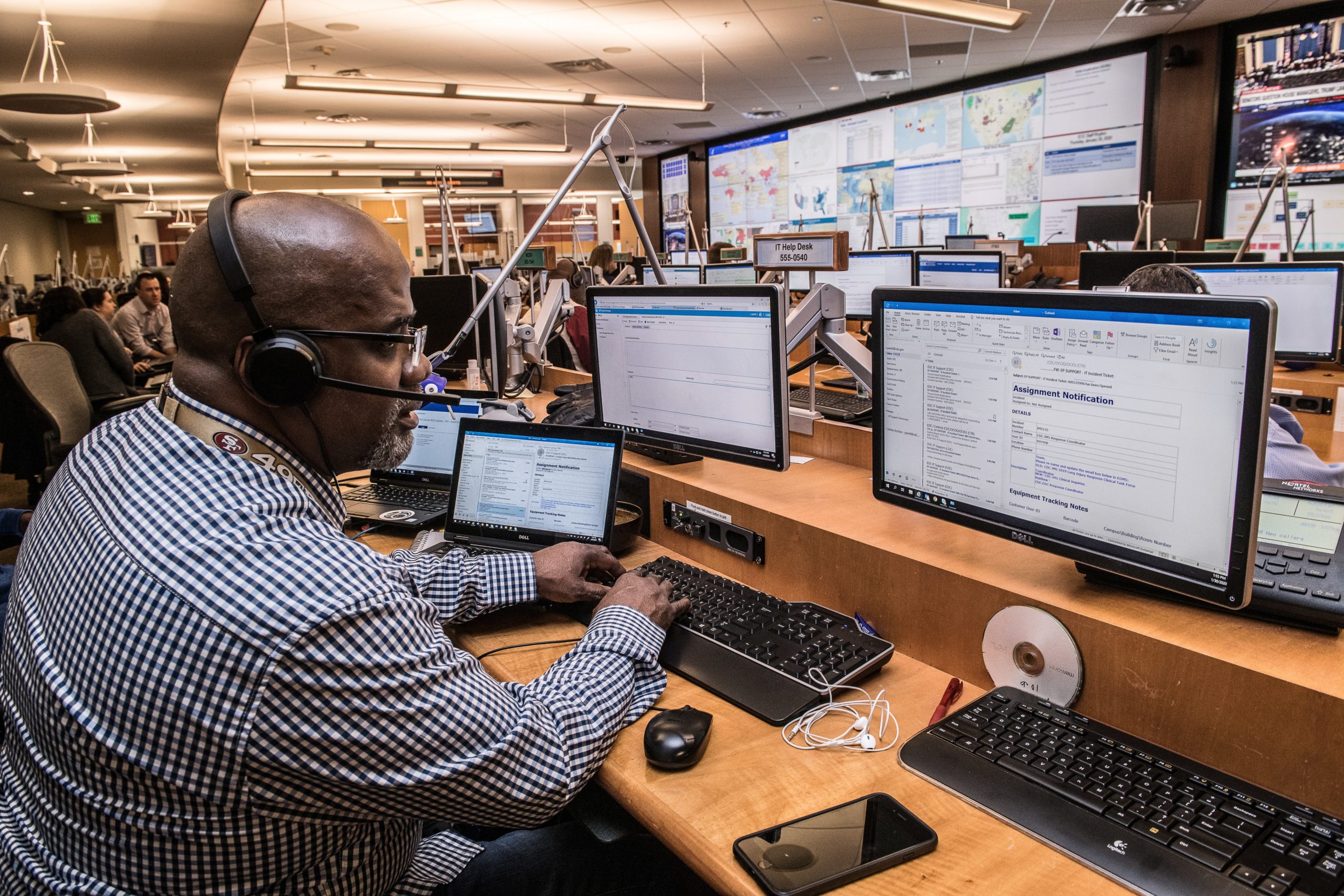
Your enterprise likely has a network operations center (NOC) and a security operations center (SOC), both of which play an important role in your day-to-day operations.
NOC vs SOC ? What is the difference, To find out, let’s answer some of the key questions surrounding NOC vs SOC.
What Is a NOC, and What Is Its Function?
A typical NOC team consists of engineers and technicians who track your IT infrastructure. The team has many responsibilities, including:
- Endpoint monitoring and management
- Incident identification, classification, and resolution
- Software installation and management
- Email management
- Backup and storage management
- Patch management
- Threat analysis
- IT performance reporting
Ultimately, a NOC team provides technical support, and it ensures an enterprise can quickly identify and resolve incidents. For example, if NOC engineers or techs notice IT issues that cause a network to slow down, they can remediate these problems before they lead to downtime that impacts an enterprise’s customers or other stakeholders. At the same time, NOC engineers or techs want to constantly improve an enterprise’s IT performance. If they find ways to upgrade an enterprise’s IT, they may prevent incidents from happening — something that may help an enterprise simultaneously lower its IT costs and boost its productivity and efficiency.
What Is a SOC, and What Does It Do?
Like a NOC, a SOC is usually an important part of an enterprise. But, whereas a NOC prioritizes IT performance, a SOC focuses exclusively on security.
Today’s enterprises are increasingly susceptible to malware, ransomware, and other types of cyberattacks, but a SOC can protect an enterprise against these attacks. A SOC team includes analysts who monitor and evaluate activity across an enterprise’s applications, networks, websites, and other systems. If SOC analysts identify anomalous activity on any enterprise systems, they will investigate it. And if SOC analysts find an enterprise has been breached, they can immediately take steps to address the incident.
Which Is Better: a NOC or SOC?
Your enterprise needs both a NOC and SOC to effectively manage all incidents, at all times. If you prioritize NOC vs SOC, or vice versa, you risk missing out on opportunities to get the most value out of your IT investments.
A NOC and SOC work in combination with one another to help your enterprise track IT infrastructure and security issues.
They also enable you to find ways to correct IT infrastructure and security problems in their early stages.
The result: dedicating time, energy, and resources to optimize your NOC and SOC can help you upgrade your IT, avoid incidents, and improve your everyday operations.
Best of all, your NOC and SOC can help your enterprise consistently meet its stakeholders’ expectations, distinguish itself from the competition, and become an industry leader.
How to Optimize Your Enterprise NOC and SOC
Your enterprise wants an effective NOC and SOC. Fortunately, there are several things you can do to get the best results from both NOC vs SOC, such as:
1. Provide Full Visibility into Data Across Your Enterprise
NOC and SOC teams need data — without it, they are unable to gain the insights they need to do their jobs effectively however to ensure your NOC and SOC teams can access data, you can provide them with tools and technologies to collect data and generate actionable insights from it.
These tools and technologies should include dashboards that make it simple for NOC and SOC teams to view your enterprise’s performance in real-time.
Additionally, NOC and SOC teams should be able to easily integrate these tools and technologies into the ones they already use.
2. Classify and Document All Incidents
NOC and SOC engineers must perform continuous monitoring across your enterprise’s systems.
That way, they can identify incidents as soon as they occur and resolve these issues before they get out of hand. In the event that an incident happens, NOC and SOC teams must track the situation as it progresses.
They require tools and technologies that foster real-time communication and collaboration among team members and ensure the right stakeholders can receive the right notifications without delay.
Furthermore, NOC and SOC teams need tools and technologies that provide stakeholders with timely, relevant, and accurate information to ensure that incidents can be resolved right away.
3. Establish Consistent Processes, Protocols, and Procedures
NOC and SOC team members must be on the same page — because, if a team member ignores a standard process, protocol, or procedure, it could cause long-lasting problems for your enterprise and its stakeholders also encourage NOC and SOC teams to develop and implement consistent processes, protocols, and procedures.
Team members should work together to determine the best ways to manage different types of incidents. NOC and SOC teams should also create reports that enable team members to monitor their performance and identify improvement areas.
4. Foster Collaboration Among NOC and SOC Teams
NOC and SOC engineers and technicians can deliver meaningful results if they communicate and collaborate with one another.
These teams can share data with each other and evaluate their respective strengths and weaknesses. Over time, NOC and SOC teams may uncover innovative ways to help your enterprise accomplish its short- and long-term goals. NOC and SOC teams may even find common tools and technologies that they can use to maximize their performance.
There may be times when your enterprise wants to improve its IT performance or address security vulnerabilities.
Yet, with an effective NOC and SOC, your enterprise can do both simultaneously, as well as limit the risk of downtime and outages, prevent data breaches, and more.
At AlertOps, we provide an enterprise incident management platform that benefits NOC and SOC teams.
Our platform is designed with enterprises in mind, and as such, automates incident management and eliminates the complexities associated with it however in doing so, our platform can help your NOC and SOC teams accelerate, simplify, and improve their day-to-day operations.
Our platform is available for NOC and SOC teams, and can be leveraged for a wide range of use-cases.